The Internet has revolutionized health care by allowing the transmission of medical examination results, diagnoses, patient histories, etc. Hospitals have been digitizing their processes and patient care for many years, following the widespread trend of digital transformation across industries.
However, such transmission may expose critical information, putting the lives of unsuspecting patients at great risk. Issues range from malware that jeopardizes system integrity and patient privacy to distributed denial-of-service attacks that disrupt facilities' ability to provide patient care and data breaches. The healthcare industry is becoming more susceptible to cybercrime because of the lack of appropriate tools for enabling providers to safely utilize electronic health information exchange.
Hospital networks have a significant security problem due to the access they have to other valuable and important files like medical, pharmaceutical, legal, judicial, nuclear, technological, and more. Patient data, including social security numbers, financial information, and health records, may be sought by cyberattacks on hospitals. Medical devices such as pacemakers, portable health recorders, computerized devices, infusion pumps, and, of course, the big target of medical records, may be hacked. Also, those who provide telemedicine care through such platforms in a web browser or mobile app should be aware of the dangers. The disruption of hospital infrastructure as a target for criminals offers opportunities for accomplishing their aims. Securing a hospital network is a must. Cybersecurity-related issues that plague the healthcare industry need an answer.
Understanding cybersecurity health is necessary before proceeding. The need for the protection of organizations from external and internal cyberattacks and the availability of medical services must be stressed.
Attention must be given to the way medical systems and equipment are operated. Confidential integrity should be maintained when dealing with patient data. The full spectrum of healthcare industry regulations must be analyzed.
The most common cybercriminal activity in healthcare involves identity theft through data breaches. Other concepts identified include internal threats, external threats, cyber-squatting, and cyberterrorism. Regrettably, the software specifications we intend to buy have been significantly modified to reduce the cost of hospital networks, and the security parameters of the systems have been neglected during their procurement procedures.
To effectively consider the huge security issue of personal data in hospital information systems, we must not only comprehend what is happening there but also develop techniques that safeguard patient data. To provide a framework for both general use and future research, a systematic review is necessary to identify themes and trends of cybercrime in the healthcare industry. In the end, we must send a strong warning message to those involved in information activities, which is necessary to prevent security holes.
Medical services must be guaranteed to be available and confidentiality maintained. Ensuring the proper functioning of medical systems and equipment, maintaining patient data integrity, and complying with industry regulations are musts. Supporting cyber health involves a variety of actions to protect organizations from both internal and external cyberattacks.
To maintain a trustworthy reputation, strong healthcare cybersecurity must be put into practice. In cases of such problems, the patients as victims may accuse us healthcare leaders of problematic data management and not only.
Is our system prepared to protect this type of data from external enemies, and do we have the appropriate infrastructure? To clarify, have we checked if any software we have installed on various public and government computer networks could be used as spyware? Look it up.
The good intentions of worldwide leaders are a fact, but addressing cyber problems needs something more than that. It's difficult or impossible to protect ourselves from unidentified criminals that surround our hospitals, which are the ones I don't trust.
Thankfully, there are methods for safeguarding against medical device hacking using encryption algorithms that are robust and ICs that are equipped with countermeasures.
A very positive step is to support a hospital's computer network shielding actions. It is necessary to conduct a systematic search through advanced databases to gather information about cyber threats in healthcare and create the necessary tools. International agencies have reported significant concerns about uncontrolled cybercrime.
Healthcare cybersecurity tools must be available, providing safe management tools. Broadcasts on cybercrime and patient privacy protection in hospital computer systems would be beneficial not only for understanding the problem but also for protecting patients from potential interception.
In the context of informing public health students, scenarios are very useful in brainstorming. Many security concerns with computer networks and uncontrolled access to them can be addressed. Before allowing unsuspecting citizens to access it, it suggests the steps we should take.
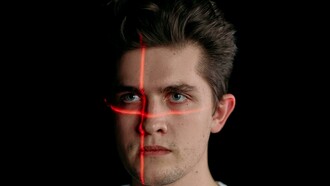
In my novel titled 'The Nuclear Network', a terrorist group manages to enter a hospital and send messages to the members of the group through its network using a (DICOM) system for coding medical information. In other words, it concealed themes in a medical image (the result of a medical examination), just as doctors do when sending a patient's diagnosis in an X-ray or scintigraphy, making it impossible for any third party to read the patient's diagnosis hidden in an image.
Note: Phishing is the most common cybersecurity threat in healthcare. Infecting an email with malicious links is known as phishing.